Introduction
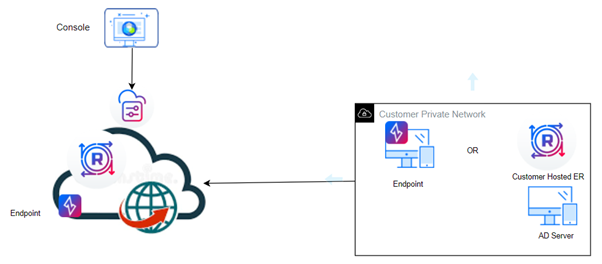
In this guide, you will learn how to integrate non-cloud hosted Active Directory in customer environments with NetFoundry endpoint groups to automatically create a client endpoint for each AD group member. The connection between the NetFoundry controllers and the on-premise / hosted AD is over the private NetFoundry ZTNA.
Normally, AD is connected through specific ports such as 3268, 389, 636 and 3269. However, while connecting on-premise AD with NetFoundy for client sync, port 389 shall be opened in the outbound direction in the LAN network that is hosting the AD server.
Note:
Above is a network diagram illustration for client sync with on-premise Active Directory via NetFoundry.
Prerequisites
A connection is required to access the AD server that is sitting in the customer private network. So, the customer is required to deploy endpoint or Edge Router in the same LAN that is hosting the AD. Let’s call this endpoint or Edge Router as “Customer AD access Edge Router/endpoint”.
Customer AD access Edge router/Endpoint should be able to reach the private IP of the AD server.
Let’s go through the setup in detail:
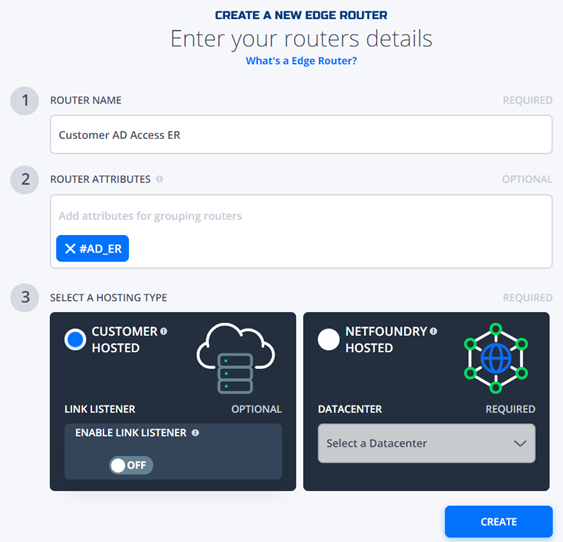
Deploy Edge Router in the Customer Premise
Deploy the VM edge router in the customer premise. Set Customer ER in the same network with AD, so ER can talk to any services in the Customer network such as AD, App Server, Database etc.
- Login into your organization console. From the left panel click Manage Networks. Then click + to create new Edge Router
- Enter your configuration settings:
- Router name: Customer AD Access ER
- Router Attributes: #AD_ER
- Select A Hosting Type: Customer Hosted
- Register VM ER with reg key
Alternatively, you can deploy a ziti endpoint. Please refer to link below for details:
https://support.netfoundry.io/hc/en-us/articles/360047133551-Create-and-Manage-Endpoints
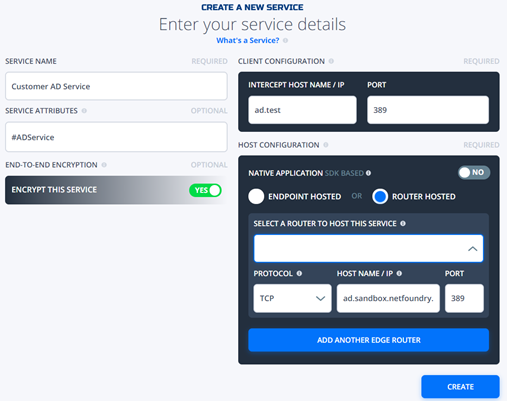
Create service to connect to AD server through specific port, e.g port 389:
- Login into your organization console. From the left panel click Services. Then click + to add a new
- Enter your configuration settings:
- Service name: Customer AD Service
- Service Attributes: #ADService
- Router Hosted: Customer AD Access ER
- Protocol: TCP
- Port: 389
Create Endpoint
Create an endpoint in the console for the Netfoundry controller to reach the on premise AD via private Netfoundry network.
- Login into your organization console. From the left panel click Endpoints. Then click “+” to add a new service.
- Enter your configuration settings:
- Endpoint name: AD Access Endpoint
- Endpoint Attributes: #ADAccesEndpoint

Keep this endpoint unregistered. Now you can integrate it with NetFoundry.
Make sure that this endpoint has an associated edge router policy to dial to the fabric routers.
Create AppWAN
In order to make sure that this endpoint can talk to this AD service, you need to create an APPWAN.
- Login into your organization console. From the left panel click Services. Then click + to add a new service.
- Enter your configuration settings:
- APPWAN name: AD AppWAN
- Service Attributes: #ADService
- Endpoint Attributes: #ADAccessEndpoint
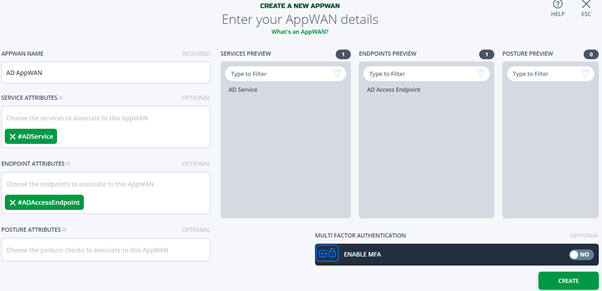
Now you can see that this endpoint can talk to AD service.
Enable Sync
Enable below sync configuration. Client sync service has to use this endpoint identity in order to talk to this Active Directory service.
Go to Manage Integration -> AD Access via NetFoundry
- Login into your organization console. From the left panel click Manage Integrations. Then click AD ACCESS VIA NETFOUNDRY.
- Enter your configuration settings:
- BASE DN:
- BIND PASSWORD:
- ACCOUNT DN:
- SELECT AN ENDPOINT:
- SELECT A SERVICE:
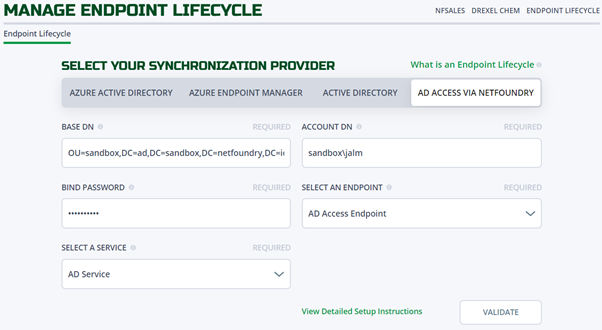
Once it has been validated successfully, you should be able to see synch settings as below.
Enter your configuration settings:
- SELECT GROUP TO SYNC FROM: Mop Development
- AUTOMATICALLY SYNC:
- SYNC DEVICES:
- SYNC TIME:
- SYNC FREQUENCY:
- AUTOMATIC CLIENT DELETION:
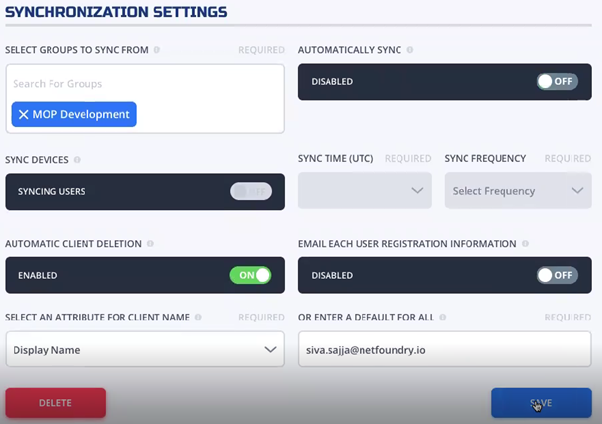
After it is successfully saved, then start AD synchronization.
To check the output, go to the Endpoint on the left and now you can see new endpoints coming from the AD.

So, you have successfully enabled a secure Ziti connection to the Active Directory using a secure connection to read group, user and sync the endpoints.